HACK Any Android Pattern Lock Using This Easy Method
A sonar works by emitting acoustic signals underwater; hence, these are the waves that travel in the marine environment, and when they collide with an object, they bounce, thus returning to the starting point. Usually, a submarine or a ship simply interprets the signals and maps the bottom recording simply to recognize the possible dangers. The technology developed rapidly during World War I and has been perfected over the years. A century later, a team of researchers from the University of Lancaster (United Kingdom) and Linkoping (Sweden) talk about hacking an Android phone by entering through its unlock pattern. To achieve this, they have previously had to convert the phone into a sonar. Nothing strange if we take into account that a smartphone does not emit sound waves, but radio waves. Hence, to solve this “problem”, researchers send sounds (inaudible to humans) through the speakers and collect (through the microphone) the echo that occurs when someone draws their unlock pattern on the screen. Then send the data to an external server, train them with machine learning (automatic learning), and in a few minutes, the system returns the password to enter into the Android device.
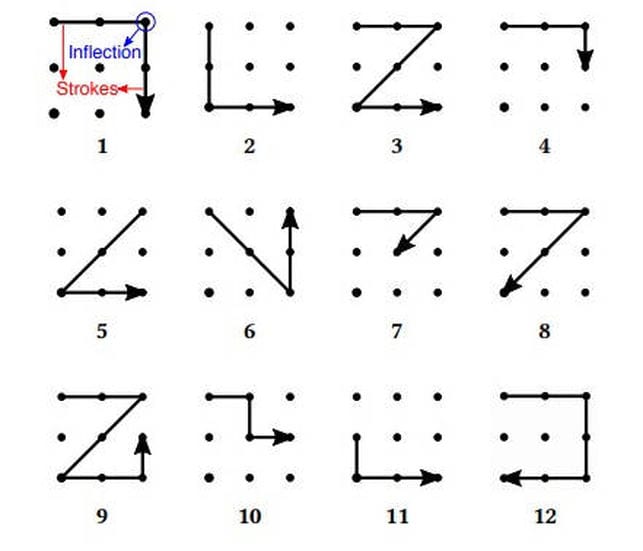
In an unlock pattern, there are 400,000 possible combinations. Researchers from both universities have relied on a previous study that ensured that only by entering 12 combinations, 20% of the Android devices that are currently present on the market are hackable. From here, they have developed and trained sonarSnoop (the name they have given to the software), getting in just four attempts to guess one of those 12 combinations. For this, the attacker has to enter the victim’s phone or at least gain access to the speaker and microphone. Only in August of last year, more than 300 apps that allowed DDoS attacks against other devices around the world swarmed the shelves of the Google Play Store. In May 2017, a team of independent researchers published that the Play Store had up to 234 applications that asked to access the phone’s microphone.
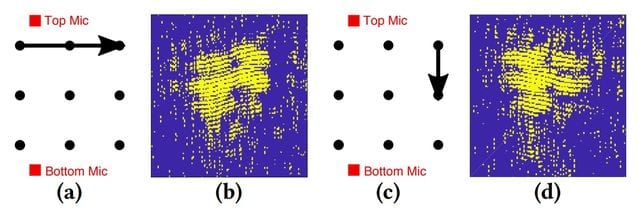
To carry out the study, “we assumed that a malware posing as a good application was downloaded to the victim’s smartphone,” Peng Cheng, one of the authors of the study, published on arxiv.org. The malware does not have to block the phone, slow it down or show permanent banners; simply, it only needs to gain access to the microphone and the speaker. “It is not uncommon for an installed application to use them; likely, the user will not notice the attack,” he continues. Once the mobile is infected, the speakers begin to emit sounds at a frequency between 18 and 20KHz so that, each time the victim draws the pattern, the resulting echo bounces off the audio waves, and the sonar effect occurs. It is not an instant technique since “the attacker will have to observe a series of unblocks”, according to Peng. Even if it only takes a few seconds to draw it, analyzing the data is longer: this is where automatic learning comes into play.
The Implications on the Internet of Things
“This happens after the data is saved and sent to a remote server controlled by the attacker,” continues the researcher. This is where the software is trained, and its efficiency is improved in the face of future attacks. When it was asked if they have already tried their technique to try to unlock protected mobile phones with an unlock code, Peng said no. That’s why they have not yet tested it on any Apple iPhones. However, the iPhones of the tech giant Apple are not impossible: another Chinese team of researchers managed to hack them through ultrasound a year ago.
Ibrahim Ethem Bagci, Utz Roedig, and Jeff Van are the other three researchers who sign the work with Peng. Beyond the fact that his technique is feasible and serves to reveal unlocking patterns, the implications are more worrisome. “If an attacker controls the audio system of these devices, then he/she can use them to observe the users (movements, positions, gestures, etc.) Therefore, this will have some security implications that should be considered”, concludes the researcher from the University of Lancaster. So, what do you think about this? Simply share all your views and thoughts in the comment section below.